calicocloud-aks-workshop
Module 9: Using alerts
Goal: Use global alerts to notify security and operations teams about unsanctioned or suspicious activity.
Steps
-
Review alerts manifests.
Navigate to
demo/50-alertsand review YAML manifests that represent alerts definitions. Each file contains an alert template and alert definition. Alerts templates can be used to quickly create an alert definition in the UI. -
View triggered alerts.
We implemented alerts in one of the first labs in order to see how our activity can trigger them.
kubectl get globalalertNAME CREATED AT dns.unsanctioned.access 2021-06-10T03:24:41Z network.lateral.access 2021-06-10T03:24:43Z policy.globalnetworkset 2021-06-10T03:24:41ZOpen
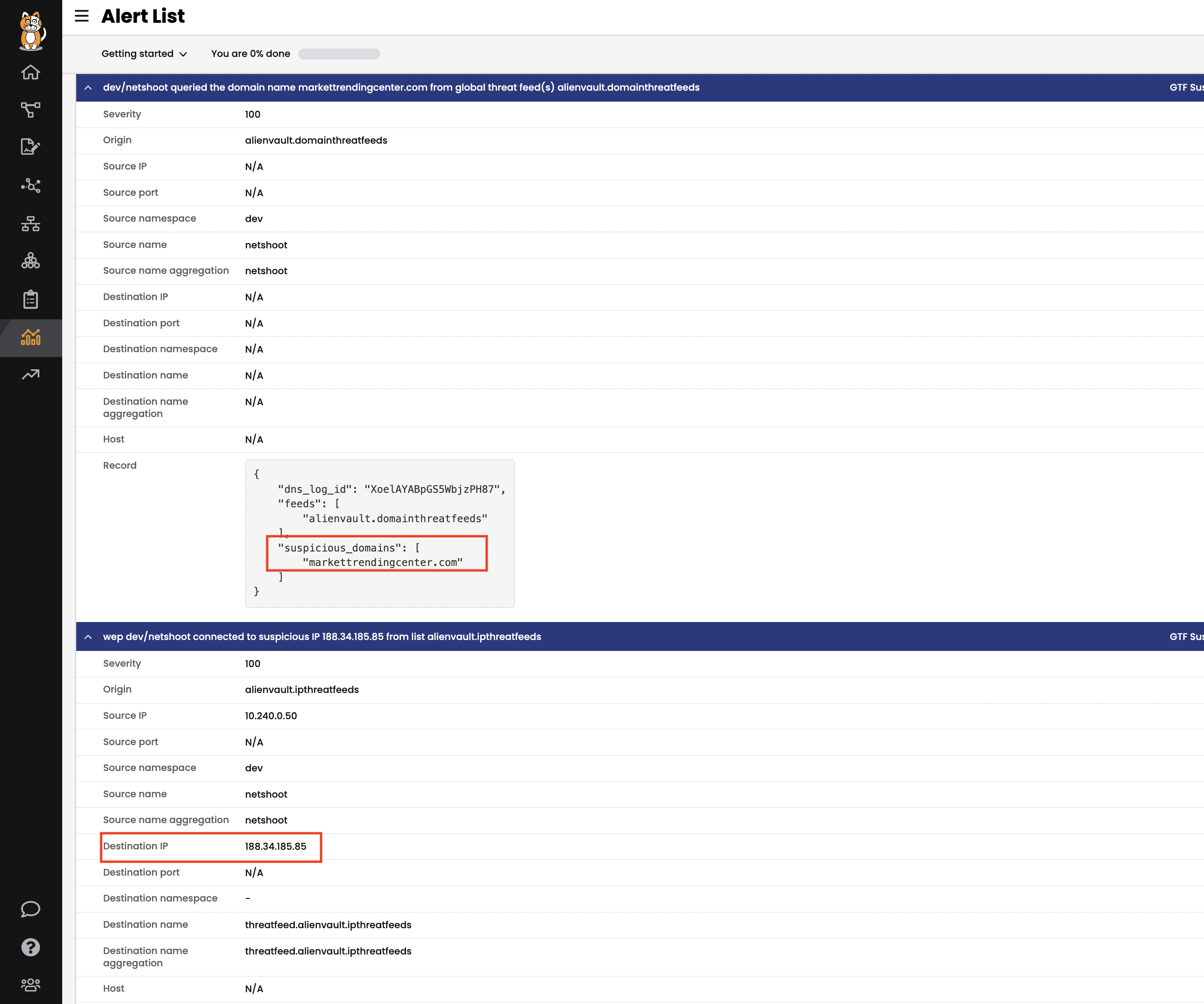
Alertsview to see all triggered alerts in the cluster. Review the generated alerts.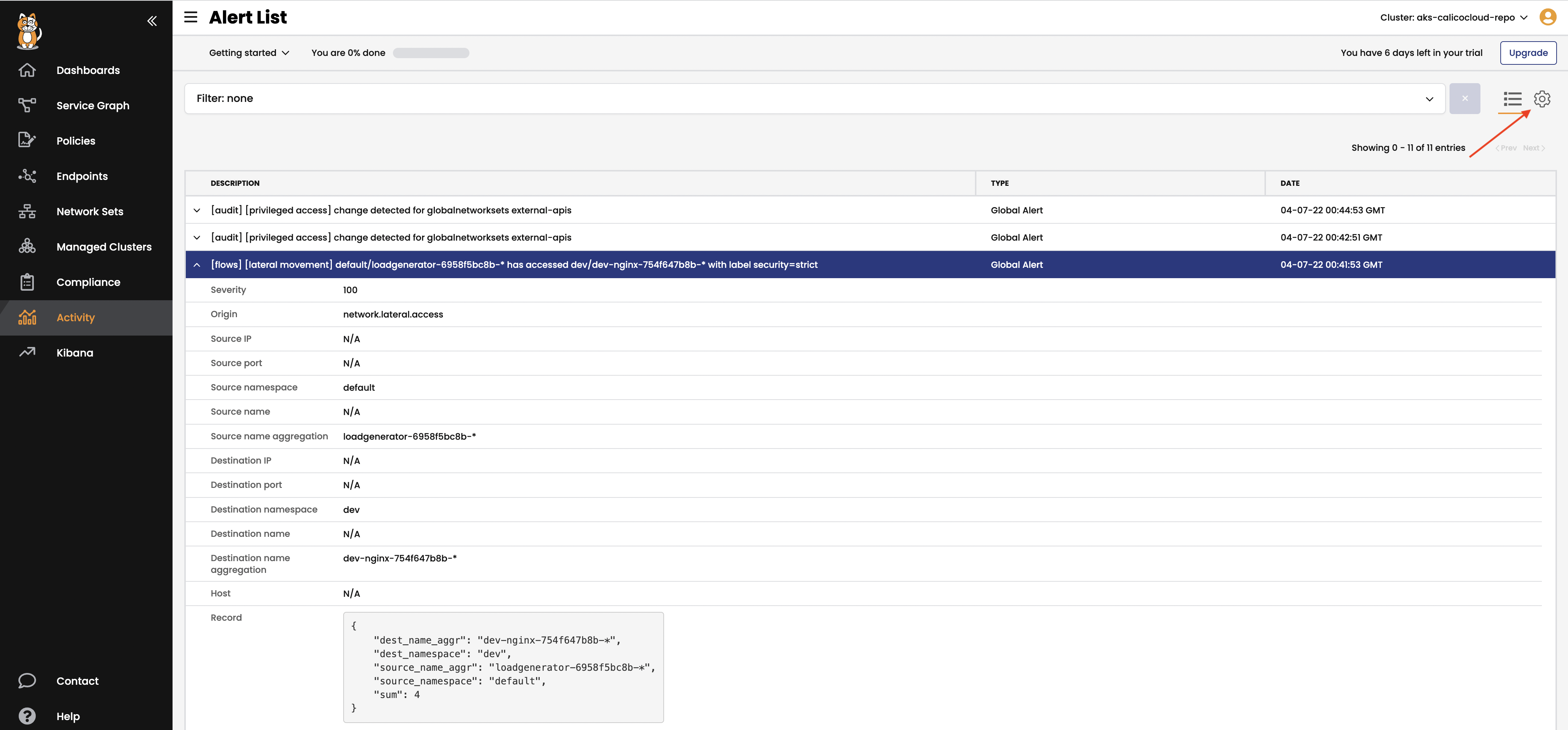
You can also review the alerts configuration and templates by navigating to alerts configuration in the top right corner.
-
Trigger dns alerts from curl demo.
# curl example.com couple times to trigger the dns aler kubectl -n dev exec -it netshoot -- sh -c 'curl -m3 -sI www.google.com 2>/dev/null | grep -i http' -
Trigger GlobalThreatfeed from known bad actors.
Calico Cloud offers Global threat feed resource to prevent known bad actors from accessing Kubernetes pods.
kubectl get globalthreatfeedsOutput is:
NAME CREATED AT alienvault.domainthreatfeeds 2021-09-28T15:01:33Z alienvault.ipthreatfeeds 2021-09-28T15:01:33ZYou can get these domain/ip list from yaml file, the url would be:
kubectl get globalthreatfeeds alienvault.domainthreatfeeds -ojson | jq -r '.spec.pull.http.url' kubectl get globalthreatfeeds alienvault.ipthreatfeeds -ojson | jq -r '.spec.pull.http.url'Output is:
https://installer.calicocloud.io/feeds/v1/domains https://installer.calicocloud.io/feeds/v1/ipsGenerate
Suspicious IPs/Domainsalerts by curl those list above. Use first entry in each threatfeed as example:# generate suspicious DNS alerts DOMAIN=$(curl https://installer.calicocloud.io/feeds/v1/domains | awk 'NR==1') kubectl -n dev exec -t netshoot -- sh -c "ping -W2 -c1 $DOMAIN" # generate suspicious IP alerts IP=$(kubectl get globalnetworksets.crd.projectcalico.org threatfeed.alienvault.ipthreatfeeds -o jsonpath='{.spec.nets[0]}' | sed 's/...$//') kubectl -n dev exec -t netshoot -- sh -c "ping -W2 -c3 $IP"Open
Alertsview to see all triggered alerts in the cluster. Review the generated alerts.